Monitoring Linux with SCOM 2012 R2 – Part 3: Installing the SCOM Agent On Linux
In our last post, we went through preparing SCOM for monitoring Linux, which included creating Run As Accounts, and associating them to the applicable Run As Profiles. In this part, we will be installing the SCOM Agent on the Linux system.
Create Linux Accounts
If you recall from our last post, we created 3 Run As accounts in SCOM. However, I mentioned that at the time of creating the SCOM Run As accounts, the actual accounts don’t need to exist on the Linux system yet. So, we will first go over how to create these accounts we referenced in SCOM, on the Linux system.
For reference, these are the Run As accounts that I created in SCOM, and the account name I used for it:
- UNIX/Linux Action Account = LinuxMonitoring
- UNIX/Linux Privileged Account = LinuxPrivileged
- UNIX/Linux Agent Maintenance Account = LinuxMaintenance
Start by logging into the Linux system as the Root user (aka. Local Administrator) so that we can create the accounts and set their permissions. Once you are logged in, right-click on the “Root’s Home” folder, and select “Open In Terminal“.
In the Terminal window, type the following commands (press Enter after each line).
- sudo useradd ACCOUNTNAME
- sudo passwd ACCOUNTNAME (Note: After you press Enter you need to type the password twice)
Repeat these steps for each of the Linux Run As accounts so that they are created.
SUDO Elevation
A new feature for UNIX and Linux monitoring with System Center 2012 – Operations Manager is the ability to use sudo elevation in the discovery and agent upgrade wizards, as well as Run As accounts. This means that the root user is no longer needed for privileged monitoring (log file monitoring, script/command execution) and agent maintenance (installation, upgrade, and uninstallation). In order to use sudo-enabled accounts for Operations Manager monitoring, the sudoers file must be configured (on each UNIX/Linux computer) to authorize elevation for the selected user account, using visudo.
The actual list of commands used for privileged monitoring or agent maintenance varies between platforms. See the following TechNet article for a list: http://social.technet.microsoft.com/wiki/contents/articles/7375.configuring-sudo-elevation-for-unix-and-linux-monitoring-with-system-center-2012-operations-manager.aspx.
In order to use sudo-enabled accounts for Operations Manager monitoring, the sudoers file must be configured (on each UNIX/Linux computer) to authorize elevation for the selected user account, using visudo.
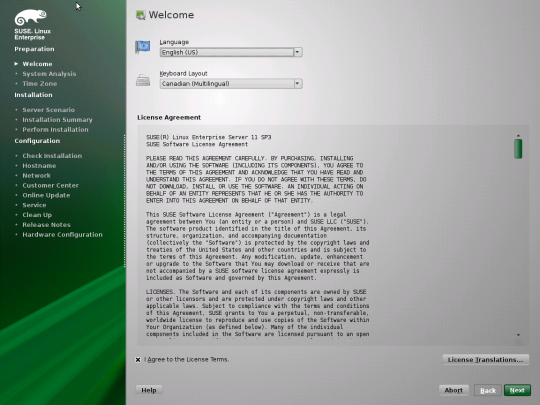
Since in my lab I am using SUSE 11, I am going to be using the following code:
#———————————————————————————–
#User configuration for Operations Manager agent – for a user with the name: monuser
#General requirements
Defaults:monuser !requiretty
#Agent maintenance (discovery, install, uninstall, upgrade, restart, cert signing)
monuser ALL=(root) NOPASSWD: /bin/sh -c cp /tmp/scx-monuser/scx.pem /etc/opt/microsoft/scx/ssl/scx.pem; rm -rf /tmp/scx-monuser; /opt/microsoft/scx/bin/tools/scxadmin -restart
monuser ALL=(root) NOPASSWD: /bin/sh -c sh /tmp/scx-monuser/GetOSVersion.sh; EC=$?; rm -rf /tmp/scx-monuser; exit $EC
monuser ALL=(root) NOPASSWD: /bin/sh -c cat /etc/opt/microsoft/scx/ssl/scx.pem
monuser ALL=(root) NOPASSWD: /bin/sh -c rpm -e scx
#SLES 9
monuser ALL=(root) NOPASSWD: /bin/sh -c /bin/rpm -F –force /tmp/scx-monuser/scx-1.[0-9].[0-9]-[0-9][0-9][0-9].sles.9.x[6-8][4-6].rpm; EC=$?; cd /tmp; rm -rf /tmp/scx-monuser; exit $EC
monuser ALL=(root) NOPASSWD: /bin/sh -c /bin/rpm -U –force /tmp/scx-monuser/scx-1.[0-9].[0-9]-[0-9][0-9][0-9].sles.9.x[6-8][4-6].rpm; EC=$?; cd /tmp; rm -rf /tmp/scx-monuser; exit $EC
#SLES 10 or 11
monuser ALL=(root) NOPASSWD: /bin/sh -c /bin/rpm -F –force /tmp/scx-monuser/scx-1.[0-9].[0-9]-[0-9][0-9][0-9].sles.1[0-1].x[6-8][4-6].rpm; EC=$?; cd /tmp; rm -rf /tmp/scx-monuser; exit $EC
monuser ALL=(root) NOPASSWD: /bin/sh -c /bin/rpm -U –force /tmp/scx-monuser/scx-1.[0-9].[0-9]-[0-9][0-9][0-9].sles.1[0-1].x[6-8][4-6].rpm; EC=$?; cd /tmp; rm -rf /tmp/scx-monuser; exit $EC
#Log file monitoring
monuser ALL=(root) NOPASSWD: /opt/microsoft/scx/bin/scxlogfilereader -p
###Examples
#Custom shell command monitoring example – replace <shell command> with the correct command string
#monuser ALL=(root) NOPASSWD: /bin/bash -c <shell command>
#Daemon diagnostic and restart recovery tasks example (using cron)
#monuser ALL=(root) NOPASSWD: /bin/sh -c ps -ef | grep cron | grep -v grep
#monuser ALL=(root) NOPASSWD: /usr/sbin/cron &
#End user configuration for Operations Manager agent
#———————————————————————————–
Within the Linux system, right-click on the “Root’s Home” folder, and select “Open In Terminal“.
In the Terminal window, type the following command (press Enter after).
sudo visudo
Navigate to the end of the file (using the arrow keys). Then press “i“, which will change the file into “Insert” mode (it should say ‘insert’ along the bottom).
Copy the appropriate code into the file. After you have copied the code into the file, press the escape key (ESC).
Note: You will see in my lab example, that I am referencing my UNIX/Linux Action Account (i.e. LinuxMonitoring). Ensure that you are referring to the correct account in your environment.
After you have pressed ESC, type the following “:wq” (without the quotation marks), then press Enter.
Note: For clarity, look at the following screenshot (at the bottom of the window).
Configure SCOM Linux Discovery
Now that we have configured the permissions within the Linux system for our monitoring account, we need to configure the SCOM Discovery.
In the SCOM console, navigate to the Administration workspace > Device Management > Agent Managed. Right-click and choose Discovery Wizard.
On the Discovery Type screen, select UNIX/Linux Computers, then click Next.
On the Discovery Criteria screen, click the Add button.
On the Discovery Criteria Wizard, add the Linux system’s name in the Discovery Scope.
After adding the Linux system to the Discovery Scope, click on the Set Credentials button.
On the Credential Settings dialog, change the Type to “User name and password” since that’s what we have configured. Type in the credentials for the UNIX/Linux Action Account (i.e. LinuxMonitoring in my lab example).
Also ensure that the ‘Does this account have privileged access?’ option is set to “This account does not have privileged access“, then click OK.
Back on the Discovery Wizard screen, now that all the fields/information is filled in, click Save.
Back on the Discovery Criteria dialog, select the Resource Pool that will be used to monitor the Linux system, then click Discover.
On the Computer Selection screen, select the Linux system, then click Manage.
On the Computer Management screen, if the deployment was successful, click Done.
In the SCOM console, navigate to the Administration workspace > Device Management > UNIX/Linux Computers. The Linux system should appear.
You can also navigate within the SCOM console to Monitoring > UNIX/Linux Computers, and check out the different views and diagrams.
Well, that covers my series and experience in using SCOM to monitor a UNIX/Linux system. I hope this was interesting and helpful for everyone.